Door access control is how modern buildings decide who gets in and who doesn’t, without relying on physical keys. Instead of handing out keys that can be copied or lost, access is managed through digital credentials that are easier to control, update, and revoke when needed.
Across many building types, door access control isn’t just about security. It affects how residents, employees, tenants, visitors, and service providers move through a space, how access is granted or revoked, and how much time teams spend managing entry behind the scenes.
As buildings become more flexible, distributed, and technology-driven, having access control that balances security with convenience becomes increasingly important.
Key takeaways
- Door access control systems help organizations and property operators manage entry more securely while reducing the friction of physical keys.
- The right setup depends on how a space is used day to day, including visitor flow, access changes, and user types.
- Reader types, credentials, and software all play a role in balancing security and convenience.
- Comparing systems side by side makes it easier to identify which approach fits a building’s operational needs.
Table of contents
- What is Door Access Control?
- Types of Door Access Control
- Types of Access Control Readers
- Access Control Credential Types
- How an Access Control System Works
- Benefits of a Door Access Control System
- Door Access Control Systems
- Conclusion
- FAQs
What is Door Access Control?
Door access control systems can be set up in different ways, depending on how access decisions are made and who manages permissions. These differences affect how flexible a system is, how much oversight it provides, and how easy it is to manage as needs change.
At its core, a door access control system checks a person’s credentials against predefined permissions. If access is allowed, the door unlocks. If not, entry is denied. This process happens in seconds, but it gives teams far more control over entry points than traditional locks ever could.
In many settings, door access control does more than improve security. It shapes how people move through the space, how visitors are admitted, and how access is managed as roles, schedules, and teams change. As buildings become more dynamic and less centralized, having a system that offers control without friction has become increasingly important.
Types of Door Access Control

Door access control systems generally fall into a few common categories, based on how access decisions are made and where permissions are managed. Understanding these types helps clarify what level of control, flexibility, and oversight a system can realistically provide..
Discretionary Access Control (DAC)
Discretionary access control systems allow individuals to grant or deny access to others. This often means a system where access is managed locally or by a small number of users with direct control over permissions.
Mandatory Access Control (MAC)
Mandatory access control uses predefined rules to determine who can access certain areas. Permissions are set centrally and aren’t easily changed by individual users.
While this model is most commonly associated with highly regulated or government environments, the underlying idea, strict, rule-based access, shows up in some commercial systems where consistency and compliance are priorities.
Role-Based Access Control (RBAC)
Role-based access control assigns permissions based on a person’s role rather than their individual identity. For example, employees in the same department may all have access to certain doors, while managers or IT staff have broader permissions.
This type of door access control is widely used in business settings because it simplifies access management as teams grow, change roles, or onboard new employees.
Cloud-Based Access Control
Cloud-based access control systems manage permissions through an online platform rather than on-site hardware alone. This allows administrators to update access, monitor activity, and manage users remotely.
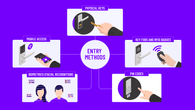
Types of Access Control Readers
Access control readers are the physical devices people interact with at the door. While they all serve the same basic purpose – verifying a credential before granting access – the way they do that can shape both security and everyday convenience.
Understanding the differences between reader types helps clarify which options make sense for a given environment.
Keypad Readers
Keypad readers require users to enter a PIN to gain access. They’re simple to deploy and don’t rely on physical credentials, which can be helpful in smaller offices or areas with limited access needs.
That said, PINs can be shared or forgotten, so keypad readers often work best in lower-risk areas or when combined with other access controls.
Magnetic Stripe Card Readers
Swipe card readers use magnetic stripe cards to grant access. These systems have been used for many years and are familiar to most users.
While reliable, swipe cards can wear out over time and are easier to duplicate than newer credential types, leading many organizations and property owners to phase them out in favor of more secure options.
RFID Door Readers
RFID (radio-frequency identification) door readers use contactless cards or fobs that communicate with the reader wirelessly. This makes entry faster and reduces wear on both cards and hardware.
Because RFID credentials are easy to issue and manage, these readers are commonly used in residential, commercial, and mixed-use buildings that want a balance between convenience and control.
Biometric Door Readers
Biometric door readers verify access based on physical characteristics such as fingerprints or facial features. Since credentials can’t be lost or shared, biometrics add an extra layer of assurance at the door.
These readers are often used in areas where stronger identity verification is needed, though considerations around privacy and user comfort may influence where they’re deployed.
Smart Locks with Access Control
Smart locks combine locking hardware and access control in a single device. They often support mobile credentials, PINs, or cards, depending on the system.
Smart locks are commonly used for interior office doors or smaller entry points where a full access control setup isn’t necessary, but flexibility and remote management are still important.
Access Control Credential Types
Different access control systems support various credential types. Here are some of the most common:
Key cards and fobs
Key cards and fobs (physical access credentials) are widely used across many building types. They’re easy to issue, revoke, and replace, but because they’re physical items, they can be lost or shared.
PIN codes
PIN codes allow access without issuing physical credentials. They’re often used for shared access points or temporary entry, such as for contractors or visitors.
PINs are convenient, but they rely on users keeping codes private, which can limit their effectiveness in high-security areas.
Biometric credentials
Biometric credentials rely on physical characteristics, such as fingerprints or facial recognition, to verify identity. Because credentials can’t be lost or borrowed, biometrics offer a higher level of assurance at the door.
They’re often used selectively, depending on security needs, privacy considerations, and employee comfort.
Mobile credentials
Mobile credentials use a smartphone as the access key. Entry is typically via an app, a digital wallet, or Bluetooth/NFC, depending on the system.
How an Access Control System Works
Step 1: A credential is presented
The process begins when someone presents a credential at the door. This could be a key fob, PIN, mobile credential, or biometric input, depending on the system in place.
Step 2: The system verifies permissions
The door reader verifies the credential’s authenticity by communicating with the access control panel on-site or a cloud-based server.
Step 3: The door unlocks (or doesn’t)
If the credential is valid and access is permitted, the system sends a signal to the door hardware to unlock. If not, the door remains locked.
This decision happens almost instantly, but it gives organizations far more control than traditional locks, where access can’t be adjusted without changing keys.
Step 4: Access activity is logged
Most systems log access events, helping operators monitor usage, investigate issues, and maintain accountability. Facilities, IT, and property teams typically evaluate how an access control system fits into existing property or building operations. Common considerations include how doors behave during power or network outages, compatibility with existing locks and door hardware, and compliance with fire and life-safety egress requirements.
Teams also look at the ongoing workload of user provisioning and deprovisioning, especially in environments with frequent staffing or role changes.
Benefits of a Door Access Control System
Door access control systems are often installed for security reasons, but their impact extends beyond keeping doors locked. In day-to-day use, they influence how people move through a space, how access changes are handled, and how much effort teams spend managing entry over time.
Improved security and access oversight
One of the most immediate benefits of door access control is greater visibility into who can enter specific areas. Instead of relying on physical keys that can be lost or copied, access is granted based on defined permissions.
This makes it easier to limit entry to sensitive areas and adjust access quickly when roles change or credentials need to be revoked.
Easier access management over time
Managing access through software is far simpler than tracking physical keys. Permissions can be updated without rekeying doors, and changes can be applied across multiple entry points at once.
Better support for changing schedules and roles
Access control systems allow organizations to align entry permissions with real work patterns. Access can be scheduled by time of day, role, or location, which helps ensure doors are available when needed and restricted when they’re not.
Reduced risk from lost or shared credentials
Physical keys create long-term risk because they’re difficult to track once they’re issued. Access control systems reduce that risk by making it easy to deactivate credentials that are lost, stolen, or no longer needed.
In real-world settings, access issues often stem from everyday behavior rather than system failures. Common challenges include tailgating at shared entrances, sharing PIN codes, or not returning credentials when access is no longer needed. Modern access control systems help reduce these risks by making it easier to revoke credentials, adjust permissions quickly, and maintain visibility into how entry points are actually used.
Whether credentials are cards, PINs, or mobile devices, access can be updated without replacing locks or hardware.
Clearer audit trails and accountability
Most door access control systems keep a record of entry attempts. These logs provide useful context when reviewing incidents, resolving access questions, or identifying unusual patterns.
Having this information available supports accountability without requiring constant monitoring.
Door Access Control Systems
In practice, door access control systems are rarely deployed all at once. Some organizations work with security integrators, while others manage installations in-house through IT or facilities teams. Many start with pilot doors or a single location, then expand over time as needs evolve. The right system often depends not just on features, but on how easily it can scale, integrate, and adapt to day-to-day operations.
Below is the side-by-side comparison of widely considered access control systems. Each solution has its own strengths depending on factors like scale, mobility, cloud management, integration flexibility, and ease of use.
| System | Best For | Strengths | Notes |
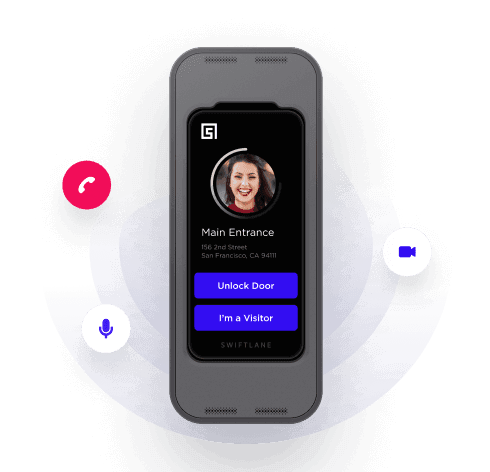
| Swiftlane | Modern buildings with flexible access needs | Mobile credentials, cloud management, video intercom | Well-rounded, flexible system with remote admin tools and scalability |
| Kisi | Cloud-first access control for growing organizations | Simple interface, strong mobile support | Good choice for teams prioritizing mobile unlock and cloud monitoring |
| Brivo | Multi-location access management | Centralized cloud admin, integrations | Often used for distributed properties and integration with other security tools |
| Avigilon Alta (Openpath) | Intuitive mobile and touchless entry | Hands-free unlock, remote control | Attractive for environments that want touchless workflows |
Conclusion
Door access control plays a bigger role in day-to-day operations than many people realize. Beyond securing doors, it affects how smoothly people move through a space, how access changes are handled, and how much effort goes into managing entry over time.
The most effective systems balance security with usability. That means choosing credential types, readers, and management tools that fit how a building actually operates, not just what looks good on a feature list. As buildings become more flexible and responsibilities more distributed, access control systems that are easy to manage and adapt tend to deliver the most long-term value.
If you’re evaluating door access control options, taking the time to compare systems side by side and consider real-world workflows can help you make a more confident, future-ready choice.
Curious how modern door access control systems are used in practice?You can explore our products and platform to see how different approaches support offices, multi-family use buildings, and commercial environments, and decide what fits best for your space.
FAQs
What is a door access control system?
A door access control system manages who can enter a building or a specific area within it. Instead of physical keys, access is granted using credentials such as key cards, PINs, mobile devices, or biometric identifiers, which can be updated or revoked without changing locks.
Are door access control systems only for large businesses?
No. While large offices and commercial buildings often use access control systems, smaller businesses also benefit from them. Even a single-entry office can use access control to improve security, manage access changes more easily, and reduce reliance on physical keys.
Do door access control systems require an internet connection?
Not always. Some systems operate locally, while others rely on cloud-based software. Cloud-connected systems typically allow for remote management and easier updates, but whether internet access is required depends on the specific system and how it’s configured.
Can access control systems work with mobile phones?
Yes, many modern-access control systems support mobile credentials. This allows residents or employees to use their smartphones to unlock doors, reducing the need for physical cards or fobs and making access easier to manage remotely.
How difficult is it to install a door access control system?
Installation complexity varies. Some systems require professional installation and wiring, especially in larger buildings, while others are designed to integrate more easily with existing infrastructure. The building layout and number of entry points also play a role.
What happens if someone loses their access credential?
One of the advantages of access control systems is that lost credentials can be deactivated quickly. Whether it’s a card, PIN, or mobile credential, access can usually be revoked without replacing locks or reissuing hardware.
Can door access control systems integrate with other security tools?
Many systems can integrate with tools like video intercoms, alarms, or visitor management platforms. Integration options vary by provider, so it’s important to review compatibility when comparing systems.
Upgrade Your Building Security
Get in touch with a Swiftlane specialist for more information on the best access control and video intercom solution for your building.