Key card technology has not changed much since their introduction 40 years ago. And still, as technology advances and behavior changes, most still use key card access control for secure building entry.
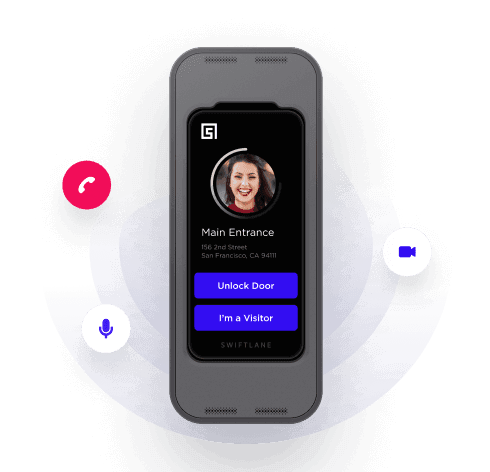
Over the past five years, facilities are beginning to shy away from physical credential systems to align with more secure, modern, and efficient technology. This includes moving access control systems from on-premise operation to cloud-based management, mobile unlock credentials, and face recognition technology.
This article details a comprehensive list of the growing pain points with key card access, which has evolved into future-proof solutions like face recognition and mobile access control.
Table of contents
- The Shift From Physical Credentials to Touchless Access
- Security Risks and Operating Inefficiencies
- Admin Management Experience
- Scalability
- Operation and Management Cost
Suggested Posts:
- Door Access Control: A Complete Guide
- Guide to Touchless Access Control Systems
- Access Control Solutions: How to Choose One
- Solve These 16 Problems With Swiftlane Office Intercom
The Shift From Physical Credentials to Touchless Access
More and more buildings are integrating touchless access control systems, especially to create safer, cleaner environments after COVID-19.
Even prior to the pandemic, using key cards as the sole method of access control was an operational burden for facility teams who had to manage them.
Some of the challenges with key cards for end users include:
- Carrying badges on a lanyard is cumbersome
- People struggle to find their key cards in their bags every time they are at the door
- When key cards are forgotten, users are frustrated when they are locked out because the process to issue a new key card or even gaining access to the building is long and time consuming
Security Risks and Operating Inefficiencies
- Key card cloners on Amazon cost only $27, making them easy to steal and clone
- Cloning a key card is without a doubt a risk to security, but the intent behind copying any access device is an act of malicious intent. This is a serious security threat to any building’s occupants and data.
- Key card operating systems only run inside the building, so you cannot manage them remotely
- Key card systems do not provide the ability to manage/remove access in real time
- Due to these constraints, there can be delays in removing access for security breaches and unauthorized individuals
- According to security experts, most companies still have a large number of key cards in circulation that belong to past occupants, which leaves buildings vulnerable to security risks
- As remote work becomes the norm, security and IT teams are facing a lot of friction when it comes to managing on-site access credentials
- Most key card systems run on insecure network communication, using HTTP or encrypted connections. This can be a weak spot for hackers to tap into. Most recently, Garmin had a major hack into their systems and had to pay out $10M in bounty.
- Legacy systems require complex network changes to the firewall, opening up more weak spots and causing a lot of stress to IT teams
Admin Management Experience
- Most key card access systems run on legacy Windows machines
- Key card systems run outdated, unintuitive software
- Admins need extensive training to learn how to use legacy systems and software
- Most companies need to hire employees with specialized technical skills to run and operate these systems
- It takes up a lot of time and effort to run a key card creation workflow: Buying new cards every few weeks, setting up printer stations for badge photos, copying card numbers, printing card numbers, etc.
Scalability
- Managing multiple buildings is a challenge on legacy systems because they only operate inside a given network connection in a building.
- Key card systems cannot handle more than a small number of doors since they need to be on the same network to operate correctly.
- You cannot remotely revoke access, which causes delays and leaks in access.
- You cannot easily pre-authorize or give out temporary access, unlike cloud-based access control systems.
Operation and Management Cost
- According to Fivestars, they had to create 2-3 key cards every day while running a 200 person office on a legacy key card system
- Recurring key card purchases because of lost or stolen cards becomes time consuming and expensive
- Key card systems require scheduled maintenance that require a full day of updates every 6 months at which time the system is completely down
- Companies typically charge $150 – $250 / hr to perform these types of updates
- Proprietary key card formats from companies like HID require purchasing special expensive versions that are only supported by those companies
- Training staff, both when a software update occurs and when there is turnover, becomes expensive, time consuming, and redundant
- Admins spend anywhere from 4 – 12 hours a week just issuing new key cards
- Because key cards are easy to clone, you need to have someone check badge photos at every entrance if you want high security
COVID-19 Considerations for Access Control
Every business is trying to minimize high-touch surfaces in order to protect their employees and visitors. Swiftlane has been busy helping companies rethink their access control post-COVID-19 by offering touchless solutions and health screening tools. It’s our priority to help enable a privacy-first touchless future, which means the future of access control needs to be touchless as well.
Find the Best Solution for Your Building
Contact a member of the Swiftlane team to learn more about cloud-based access control solutions.