The disruption from COVID-19 has changed the way we will approach physical security in 2023 and beyond. From industry expertise, research, and projections, we’ve put together the 5 major access control trends for the coming year:
- Mobile Access Control
- Cloud-Based Security
- Multi-Factor Authentication
- Biometric Technology
- Subscription-Based Business Model
Building a resilient facility and security strategy that withstands adversity has never been more important. Altogether, the 5 major access control trends will translate into the following applications:
- The Rise of Touchless Access Control
- New Access Control Technology
- Access Control Convergence and Integration
Table of contents
- Access Control Technology Concerns
- Access Control Trends in 2023
- Mobile Access Control
- Cloud-Based Access Control
- Multi-Factor Authentication
- Biometric Access Control
- Subscription-Based Business Model
- The Rise of Touchless Access Control Systems
- New Access Control Technology
- Access Control System Convergence and Integration
Also, read
- How Facial Recognition Works
- Best Face Recognition Door Locks
- Best Cloud Based Access Control Systems
- Face Recognition Access Control Systems
- 10 Benefits of a Cloud-Based Access Control System
Access Control Technology Concerns
The past decade has been a strong host for innovation in access control technologies. Typically, access control has been a slow moving industry, but there has been a huge shift due to clear customer demand and need for better access control experiences.
A 2019 survey of 473 security directors, managers, and consultants conducted by HID Global and Security Management magazine identified the top access control concerns at that time:
Integration with legacy systems (45%)
Taking advantage of features in new technologies (39%)
Protection against increasing vulnerabilities (38%)
User convenience and throughput at entrances (36%)
Making physical access processes simpler with digital administration
Meanwhile, the 2019 year-end report from Imperial Capital, which tracks the security industry, concludes that the identity and authentication sector exceeded all other security sectors between 2018 3Q and 2019 3Q, with a 35.1% gain in company valuation multiples.
According to that report:
Identity and authentication technology, from software to biometric equipment, is continuing to mature, as evidenced by its increasing adoption by an array of government and defense programs in response to increased security threats, international identification programs, as well as increased cloud-based hosted access and ID systems being installed by integrators for both government and commercial sites. The acceptance of analytics, behavior and related biometric modalities … have all played a role in the 50% increase in this sector’s valuation since December 2015.
Access Control Trends in 2023
Security Industry Association’s most notable 2021 Security Megatrends include Touchless and Frictionless Solutions, Facial Recognition, Cloud Computing, and a move to Service Models. Below, we have compiled our own projections for the top 5 access control trends we can expect in 2022 and 2023.
1. Mobile Access Control
Companies are rapidly adopting mobile access control.
44% of office workers note that the pandemic has made access control an even more important issue. In 2019, a survey by HID estimated that 54% of businesses have upgraded or will upgrade to a mobile access control system in the next 3 years. With the clear rising necessity and growth of mobile access, we can assume that well over half of the projected businesses will be transitioning away from legacy systems in the coming years, if they have not already done so.
Research firm IHS Markit has reported that mobile based credentials are the fastest-growing access control product, up about 150% in growth rate between 2017 and 2018. It predicts that more than 120 million mobile credentials will be downloaded in 2023.
The use of mobile based credentials is the organic evolution for the physical security and access control industry. 93% of the entire U.S. population uses a smartphone, most of which have their device on their person all the time. They are undeniably ubiquitous. Alternatively, key cards are inconvenient, clocking in as the second most forgotten item. Since most key cards are unencrypted proximity RFID cards that can be cloned easily, mobile credentials also offer a more secure solution. Convenient and more secure, we are seeing a strong shift towards mobile access control like various companies such as Swiftlane, Kisi, Proxy, Genea, Openpath and many more.
2. Cloud-Based Access Control
Cloud-based access control seeing adoption in midsize and enterprise companies.
Physical security has been a late adopter for the cloud, particularly in midsize and enterprise companies. Most company systems today, however, run on cloud-based systems. You name it and that system runs in the cloud, it’s just not obvious: messaging, email, sales CRMs, marketing tools, productivity tools, IT infrastructure, website hosting.
Physical security is seeing a strong shift towards cloud-based access control, due to huge benefits provided in terms of operational improvements, higher security and easy multi-site management of access to reap the benefits of limitless scalability.
Multi-site access management has previously been a seriously sub optimal experience. For example, if an employee is visiting a different branch office, it would require notification multiple days in advance in order to prepare for their arrival in terms of security and access. Manual processes like these, in addition to being inconvenient, result in higher leaked credentials and security inconsistencies. The adoption of cloud-based systems has become an emerging trend due to the ability to manage multiple sites under a single system. Access levels can easily be managed across all sites. Moreover, it’s possible to manage a global infrastructure without compromising security or convenience. In fact, security is strengthened and convenience is higher in this environment.
Cloud-Based Access Control Benefits
- The system can scale with the needs of the organization
- Constant security updates that can be rolled instantly
- Zero down time
- Mobile first access management
- Hundreds of buildings managed from a central location
- Real-time and remote grant or revocation of access
- Constant data backups
- Fast product evolution
Cloud vs. Edge Computing
That raises the issue of which access control data gathering, analysis, and storage model will prevail in the future: cloud computing (which when farmed out to a third party becomes known as access control as a service) or edge computing.
In cloud computing, data is gathered and analyzed in a central location, offering the advantages of power and scalability. It also offers the convenience of managed service and automatic software updates.
IHS Markit has forecast steady demand for a SaaS model for access control, especially among new users such as small and medium-sized businesses. It would not be surprising to see more proptech solutions trending towards this increase in demand, as well.
In edge computing, data is gathered and analyzed on the device itself–be it camera, card reader, alarm panel, etc. Edge computing’s major benefit is much faster processing time–critical, for example, in telling an autonomous vehicle whether to brake–and suitability for remote applications.
Edge computing, a concept that has existed for years, is hot in 2020. In fact, it has been estimated that by the end of the year, 40% of the data on the Internet of Things will be stored, processed, examined and applied near to or at the edge of the network.
Rather than being in competition, however, cloud and edge computing complement each other, and are likely here to stay for at least the mid term for use in access control technology. Cloud-based access control offers convenience and cost-effectiveness among other advantages, while edge computing suits remote applications, and, as Axis Communications puts it, saves materials and labor costs (no wiring) and simplifies future changes.

Smart GSOCs
Today’s global operations centers (GSOCs) require large rooms filled with dozens of screens streaming video and access control feeds from all access points. The rapid evolution of mobile phones, cloud connected devices, and anomaly detection software will avoid the cost and complexity of GSOCs. Anomalies will be pushed to security managers directly on their phones. Computer vision will detect an active shooter with a gun and immediately notify security teams directly on their phones anywhere around the globe. The result will be higher security in real time.
Automatic Anomaly Detection
With improvements in AI and Machine Learning, suspicious activity can be detected instantly. If a person normally badges between 9-5 PM on weekdays, a badge scan at 10 PM will instantly generate an alert for security teams. Security guards don’t have to be glued to the computer screen, watching every single access event across all doors. Instead, their time can be freed up to patrol and observe the space around them. They can be automatically notified of events, right on their phone, and they can respond to them in real time.
Presence control
Covid-19 is helping shift the access control paradigm to a presence control paradigm; that is, as important as it is to know who is entering your organization’s spaces, it is becoming equally important to know where staff are within those spaces, to ensure physical distancing, de-densify common areas, be prepared for safe evacuation, and so on.
Real-Time Location Services
Real-Time Location Services (RTLS) enables organizations to track the locations of all people in a facility. RTLS also optimizes space use, provides for enhanced asset-location awareness, and enables more efficient use of lighting, HVAC, and other resources.
RFID, wifi, and Bluetooth, infrared, and cellular are among several technologies used to track individuals, as well as assets. Real Time Networks offers a good comparison of the technologies. The Hong Kong government is using the technology, via wristbands, to geofence people who have tested positive for covid-19 and ensure that they don’t break quarantine.
RightCrowd is one provider that has active applications in the field, including in an open-office environment and at high-security areas of an R&D facility. RightCrowd uses Bluetooth technology as its virtual backbone.
A forthcoming report by Market Trends analyzes trends and drivers in the RTLS market, forecasts growth through 2029, and compares solutions by such companies as Zebra Technologies, Impinj, CenTrak, and Versus Technology. Forecasts by other companies break down RTLS use in different markets, including sporting events.
3. Multi-Factor Authentication
The convergence of digital identity with physical identity.
Mobile credentials are also being used for both multimodal and multi factor authentication. (Multimodal authentication can mean proving identity/gaining access with at least two separate biometrics, or allowing access via use of any one of various credentials, such as a keycard or PIN. Multi-factor authentication means having to prove identity/gain access via at least two methods or credentials–including something you know, have, or are)–such as fingerprint and a password.)
Multi-factor authentication is now widely used in digital access. For example, when an employee logs into a company email or another sensitive website, the business requires another method to verify identity via a one-time token via SMS or another authenticator app.
Two-factor authentication has been required of physical security for certain verticals, like oil, gas, and power plants as part of NERC compliance in utility industries and other critical infrastructure. Now, it is also becoming available to other corporate customers who want a more advanced level of security. With the emergence of multi-modal readers that support key card, mobile, pinpad, and biometrics all in one, there is increasing availability of using two-factor authentication for wider deployments.
Both multifactor and multimodal approaches have significant benefits. Multifactor authentication is more secure than single-factor authentication. It also helps organizations to feel more comfortable using single sign-on, and single sign-on is a favorite of users because it greatly simplifies network access. Further, multi-factor authentication may be required by regulation to handle personal identifying information. Multifactor authentication is frequently used by consumers when changing account passwords or performing online transactions; they will be cued to enter a PIN sent via SMS text or email, for example, to verify identity. These are called push notifications, and they are a favorite of research and analyst company Gartner. Gartner predicted that 50% of enterprises using mobile authentication would adopt it as their primary verification method by the end of 2019.
Multimodal Authentication
Multimodal authentication that requires two separate biometrics is far more secure than a single biometric, but more costly and time consuming. Multimodal authentication that requires a choice of several authentication credentials is less secure but far more convenient; for example, if you forget your keycard you may be able type a PIN into a keypad.
Blockchain Authentication
Meanwhile, blockchain technology is emerging as a contender in the authentication sweepstakes. Some have hailed it as the underpinning of all security applications in the near to mid-term future.
Blockchain use cases have sprouted in almost every security application, and access control and authentication is no exception. Researchers have already established proof of concept, so it is likely that some access controls systems will be based on distributed ledger or blockchain technology. According to research done at the University of Saskatchewan, “By exploiting Hyperledger Fabric and Hyperledger Composer potential we have implemented a tamper-proof access control application based on permissioned blockchain for managing access permissions on physical places.”
Blockchain also facilitates scaling access control and authentication. As Robin Gaal explains:
An interesting aspect is that the blockchain can be used as an authentication provider. Imagine you can authenticate yourself at government services, banks, airports and other services with only one identity using blockchain technology. Using their key-pair, users register their identity on the blockchain. This registered identity is a piece of information that contains hashes of several identity related attributes. For example their name, governance registration number, fingerprint or other biometric information. After that such a user can go to a recognized party, which verifies the hashes earlier registered on the blockchain and let the recognizing party “sponsor” that piece of information as the truth on the blockchain. Other parties which trust the particular recognizing party can now trust the identity on the blockchain and use it as an authentication or identification mechanism.
4. Biometric Access Control
Face recognition is being used for touchless access control, replacing fingerprint access.
Many companies are rushing to bring the face ID style phone access to building and facility access. Using facial recognition access control provides a modern, touchless access experience.
Biometrics have existed at the periphery of access control technology for decades, limited by high cost, accuracy issues, privacy concerns, and other issues. But with prices dropping, quality improving, and privacy concerns not at the fore, it has become a viable access control technology in the Covid-19 era. One forecaster predicts that “Contactless biometric technology will ride the wave created by the Covid-19 pandemic to a CAGR (compound annual growth rate) of 17.4% from 2020 to 2030, with the global market increasing five-fold to reach $70 billion.
Among the key takeaways: facial recognition will grab the largest market share as it becomes widely implemented for both identity verification and access control; other technologies to experience growth include iris, palm, vein, voice, and touchless fingerprints; and demand for contactless biometrics among government agencies will surge due to public safety concerns.
Facial recognition systems have traditionally been expensive and unapproachable. Expensive installation requires significant integration costs in order to work on top of legacy systems. Enrollment process was cumbersome and required a queue of people for enrollment at the individual stations. With advance and innovation in biometric access control, installation is cost effective and can compete with the cost of alternative key card systems. Instant self enrollment and simple integration has made facial recognition more accessible than before. Cloud dashboards are allowing admins to centralize access management.
In the COVID-19 world and beyond, face recognition will be a critical form of authentication, given the touchless experience. Past implementations of face recognition access control technologies suffered from poor accuracy, anti-spoofing issues, and lack of privacy controls. But advances in recent years have catapulted the technology into the mainstream. Critical requirements for a facial recognition access system include the following:
- 2D and 3D checks for face recognition
- Learning continuously over time to adapt to changing face features
- Prevent attempts to fool it using a photo or video of a person (anti-spoofing)
- Easy enrollment
- Works well with various demographics
- Strong privacy controls to limit the use of the data
5. Subscription-Based Business Model
Shift to a subscription-based access control model from a one-time hardware sales model.
In Behind the Cloud, authored by Salesforce’s Chairman & CEO, Marc Benioff details his journey to create a new industry: subscription-based CRM. This opened the door to the subscription-based model for businesses as opposed to the legacy network systems. Legacy CRM software and networks required years to integrate, constant maintenance and manual updates. They were tailored with specifications for each individual enterprise it served, which subsequently made the system inflexible, clunky, time-consuming and incredibly expensive. Mr. Benioff created a model that rectified the issues that built an entire new industry based on end user control and monthly subscription to foster flexibility and accountability. Consequently, this model is used in the majority of business today.
The same story rings true with access control technologies. Traditionally, access control has been a hardware sales driven business model. You buy readers, key cards and panels from distribution and have an integrator assemble and program the on-premise server. Updates need to be manually programmed, and an IT staff is needed for operation. Times change, as has our culture and security landscape. And such, this model is now being phased out and replaced by subscription-based access control operated from the cloud to give end users the control and flexibility they want.
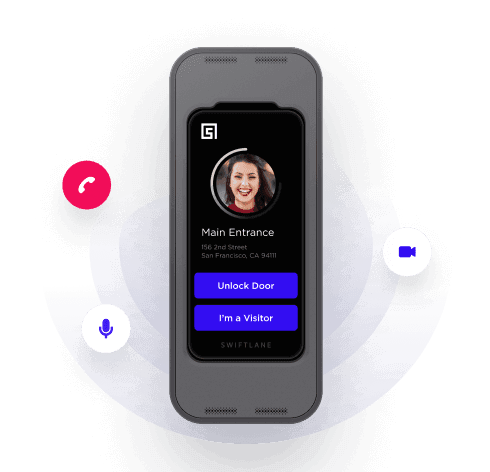
Integrated user access and visitor access
Modern apartment intercoms and business intercoms combine access for users into the same hardware and software. The same hardware can be used to provide:
- Video intercom calls for visitors
- Face recognition access for users
- Mobile and Key card access for users
- PIN based temporary access
The Rise of Touchless Access Control Systems
A report by ABI Research sees things differently in light of the Coronavirus pandemic; it projects a $2B drop in revenue in shipment of biometric devices through 2020. But there are two exceptions: face recognition and iris matching. As reported by securityinfonews.com: “face and iris recognition have emerged as key technologies allowing authentication, identification, and surveillance operations for users and citizens wearing protective headgear, face masks, or, with partially covered faces. These elements, which used to be the bane of face recognition algorithms in the past, have now been integrated into algorithm developers’ value propositions.”
Another analysis, which takes covid-19 into account, offers yet another sunny forecast for face recognition in access control. Face Recognition using Edge Computing Market Intelligence Report – Global Forecast to 2025 – Cumulative Impact of COVID-19 predicts a 20% CAGR from 2019 to 2025, based on the “privacy, bandwidth, and other potential benefits of performing facial recognition directly on edge computing devices.”
However, the growth in edge biometrics is not expected to impair the market for cloud-based biometrics security as a service. According to the report, “The anticipated growth in cloud-based biometrics services would seem to suggest that the growth in edge facial recognition will not come solely, or perhaps even mainly from cannibalization of applications hosted on centralized digital IT infrastructure.”
Access Control Changes for Hygiene and Physical Separation
Around the world, offices, factories, retail stores, restaurants, stadiums, theatres, museums, libraries, hotels, banks, and pretty much every type of facility that houses workers has sat empty, or almost empty, for months. Companies will have to gradually coax nervous staff back on site, and foremost in that effort will be safety assurances, policies, and protocols. Access control may become more granular, perhaps with low security doors removed or propped open, corridors altered, and frequently touched barriers minimized.
But safety measures don’t have to mean abandoning security. Stanley Security Solutions recommends such measures as modifying hours of operation in access control systems to reflect current policies as well as auditing access privileges and taking a zero-trust approach to access, if feasible. For initial entry into a building or discrete zone or facility, BOMA International suggests limiting access points to the building–one entrance and one exit if possible. In addition, companies can route visitors at lobby desks with separate paths for “in” and “out.”
While businesses look at long-term solutions to their access control technology, they are taking low-cost short-term measures as they see how the pandemic plays out. For example, instead of using office closures to install touchless access control systems, businesses–which may well be reducing their square footage anyway as return to work remains in doubt–are placing sanitizer and/or napkins/paper towels on both sides of doors; testing personal keychains or hook-like devices that can be used to turn door handles, push elevator buttons, and flip on light switches; and distributing masks and disposable gloves.
Access control system data can also be audited to perform contact tracing for individuals who test positive for Covid-19. One newly created solution, called the COVID-19 Exposure Report Tool (CERT), represents a partnership between Convergint and Detrios. According to securityworldmarket.com, “Time frames can be specified before and after a COVID-19 positive individual entered an area. Administrators can also receive a CSV export of those potentially exposed to COVID-19, with the ability to obfuscate COVID-19 positive or exposed individuals’ names, to protect people’s identities and calculate the magnitude of exposure.”
At the request of McCormick Place in Chicago, Genetec offers a similar system. As Campus Safety reports, “The new reporting function is said to correlate physical proximity of an infected individual with other employees and badged visitors based on the use of the access control system. A report can quickly be generated to correlate access events by time window to identify people who are at increased risk of being in contact with contaminants or contagious individuals, according to Genetec.
Access control companies, video providers, and data analytics companies are each creating systems to address Coronavirus by monitoring occupancy of work sites to ensure physical distancing requirements. Genetec, and VCA Technology have versions, each based on different technology. And some companies are considering remote security operations centers.
New Access Control Technology
It’s hard to believe that smartphones didn’t exist in 2006. They have transformed computing in myriad ways, from communication to travel to shopping to entertainment to education to security and beyond. But handheld devices can disappear as quickly as they emerged. Already, smartphone capabilities are migrating to wristwatches, earbuds, belts, and even smart clothing. Circuits are getting smaller, prices are dropping, and the quest for convenience and style continues unabated.
For access control, wearable devices dispense with having to pull your phone out to open a door; instead, you can wave a watch, a necklace, or some other device. One day soon, that may seem too onerous as people start tattooing, implanting, or injecting computer components, enabling access control with a wave of the hand.
Sound far-fetched? Elon Musk is testing implantable neural network technology on monkeys through laser surgery. Smaller companies are seeking the same goal through technologies such as inserting a stent through a vein in the back of the neck, which then embeds 16 metal electrodes into the blood vessel’s walls from which neuronal activity can be recorded.
Futurist Scott Klososky, when confronted with skepticism whether anyone would agree to implant neural technology in their child, had the following response: “If all the other children have been ‘augmented’ and are reaping huge advantages, parents will naturally want to keep their children on an even playing field.”
Compared to all of the other capabilities presented by implantables, access control is relatively minor. But consider how implantables can become a form of universal access control for an individual once he or she uploads his or her personal software “key” in the cloud.
Access Control System Convergence and Integration
Not 20 years ago, IT departments would blanch at the prospect of running physical security components–”bandwidth hogs”–over corporate systems. But with widespread installation of fiber-optics and the explosive growth of bandwidth and throughput rates, it’s a rare company that fails to integrate all security components, both physical and cyber, into the corporate network.
Digital identity has seen a huge amount of innovation over the last decade, starting with single sign-on experiences like “Facebook Login” and “Google Login ” in the early 2010s. Using single sign-on, users don’t have to create shared passwords across hundreds of untrusted sites and risk their passwords getting stolen. Around 2015 brought large adoption of this technology for enterprise and commercial access. GSuite Sign on, OKTA, OneLogin, and similar companies have paved the way for large adoption of SSO in the enterprise access space. This allows companies to enable or disable access to hundreds of websites and software in one shot. The next advance will be convergence of identity between digital and physical access. The same SSO providers will be used for granting access to individuals for building and physical access, instead of relying on on-premise software maintaining outdated records of access, and remaining vulnerable to access by ex-employees.
Cyber and physical integration has had, and will continue to have profound implications for access control technology. Once separate systems, physical and cyber access controls often function seamlessly. The same face recognition technology that opens the door of the office suite also integrates with a camera that allows a guard to confirm your identity and with your PC to give you network access. This trend is expected to only accelerate in the future.
In fact, 36% of access control installations in educational settings now include video or intrusion detection systems. An integrated, cloud-based access control and video management solution allows users to seamlessly monitor access activity and link events at doors with integrated video.
A survey by HID Global and ASIS International enumerates three major benefits of access control integration. First, users are eager to adopt converged credentials. Second, users are less likely to lose combined credentials. Finally, the single credential reduces the need for strong passwords, which are notoriously difficult and frustrating to remember.
Tools4Ever Managing Director Tim Mowatt describes other advantages of integrated access management:
Provisioning will be far more rapid since transferred identity data will help to create accounts and configure access levels immediately. Continual improving integrations will provide administrators and managers with far more granular control during initial setup, active management, and deactivation.
Also, increasing connectivity allows centralized management at the source of the authoritative identity data and pushed easily from there. At the same time, systems and applications will better incorporate identity data to enforce a given user’s permissions within that resource.
Perhaps the only thing holding back integrated access control is the lack of departmental convergence or cooperation between physical and cyber security departments. In fact, a 2019 study by the ASIS Foundation shows that only 24% of companies in the United States, Europe, and India have converged physical and cyber security, and there is scant evidence that the number is increasing.
The HID/ASIS report adds that while security directors report that they work with IT departments to establish security best practices for their facilities (61%) and to look for new technologies cooperatively (55%). 20% report that there is little or no overlap between physical security and IT.
Asked in the HID/ASIS survey to rate the level of authority on decisions to upgrade physical access control solutions: 46% said IT was fully consulted and another 22% said IT was involved in either the final recommendation or the final decision. 10% said IT had no influence.
For 28% of respondents, “Integrated physical and logical access control” was selected as the top technology advancement that would have the most impact on improving the organization’s overall access control system.
Need More Info?
Still have questions about cloud based access control systems for your facility? Contact a Swiftlane expert to navigate your options and the best solution.
About the Author
Michael Gips, JD, CPP, CSyP, CAE is a collaborative physical/cyber security advisor, and currently serves as the principal of Global Insights in Professional Security, LLC, a firm that helps security providers develop cutting-edge content, assert thought leadership, and heighten brand awareness in a crowded marketplace.