Every day, billions of people worldwide unlock their smartphones using face recognition access control. That same technology is increasingly used in access control systems for buildings. Whether it’s at the front door of a small multi-tenant apartment building, the lobby gates of a large office tower, or the reception of a salon suite, a facial recognition entry system offers a quick, efficient, and hands-free way to screen authorized people to enter.
With facial recognition, your building gets a modern and secure replacement for PIN codes or physical authentication devices like metal keys, key fobs, and ID badges. However, facial recognition can also work alongside those tools as well.
As more and more facility managers and property owners are gaining interest in this tech, we’ve put together this guide to cover your need-to-know information. We discuss the technology and how it works, as well as good use cases. We also explore its potential limitations. At the end, we share information about ten top-tier product manufacturers of facial recognition door access systems.
Table of Contents
- What is Facial Recognition Access Control?
- Jump to: Ten Top-Tier Makers of Facial Recognition Access Control
- Frequently Asked Questions
- More About Swiftlane
What is Facial Recognition Access Control?
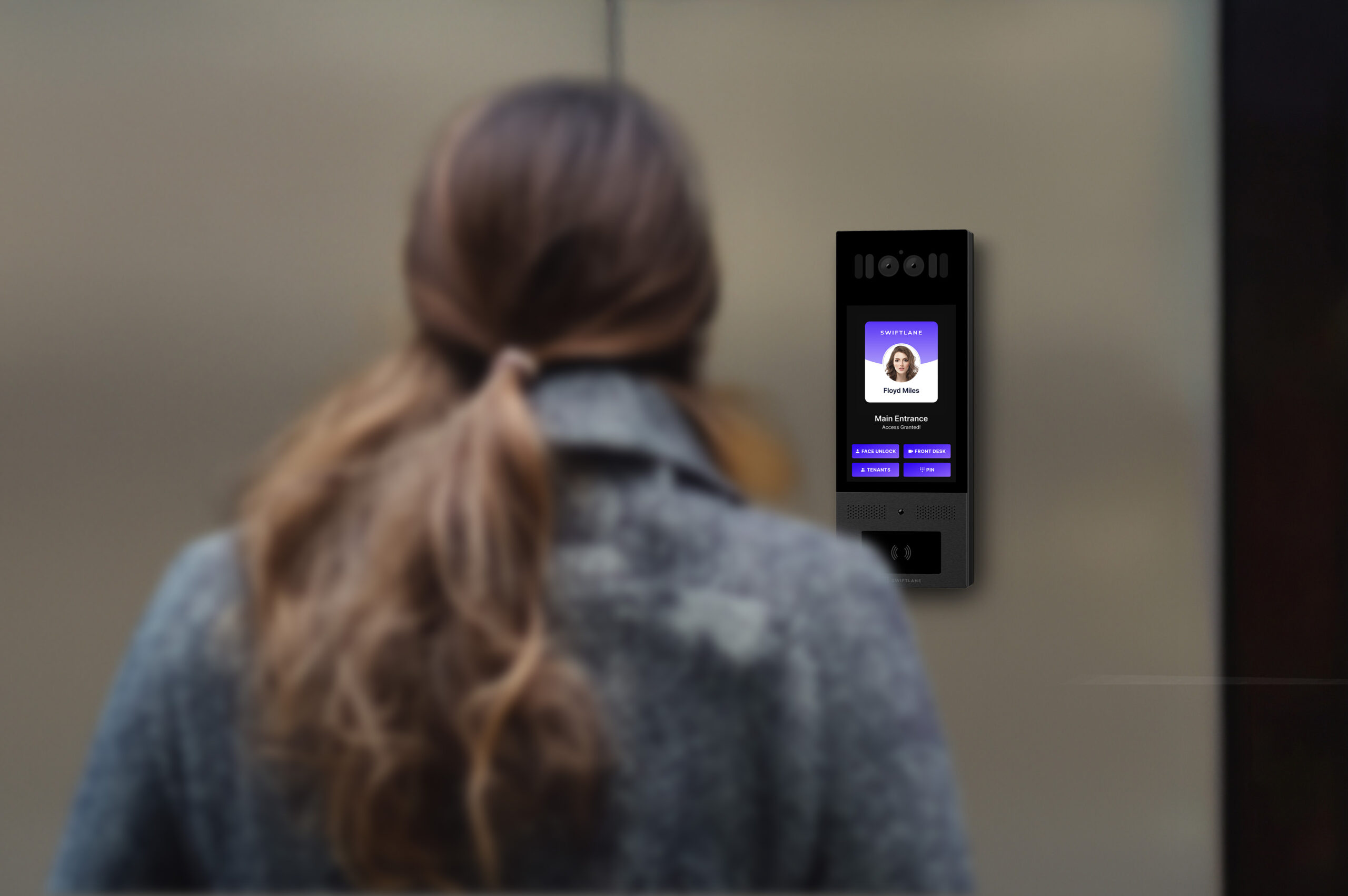
Facial recognition for access control is a security system that uses biometric technology to identify individuals based on their facial features. Instead of traditional access methods, which can be shared, lost, or stolen (e.g., keys, PINs, or cards), it grants or denies entry by analyzing unique facial patterns using image processing algorithms and cameras. These systems are widely adopted for secure, touchless, and efficient access management.
Applications of a Facial Recognition Door Lock System
Residential Buildings: Enhance home security with keyless entry and visitor verification. Building residents just look at the building intercom, and the door unlocks. Meanwhile, the same intercom camera can provide a video link between visitors and the building’s residents to provide remote entry to authorized guests.
.Corporate Offices: Use face recognition access control to operate gates and turnstiles in an office building lobby without employees having to fish out physical ID badges. Secure access to restricted areas, data rooms, and provide employee entry management in different zones with different authorization levels.
Healthcare Facilities: Controls access to sensitive areas like operating rooms or medicine storage.
Airports & Border Control: Facial recognition is increasingly used by the Transportation and Security Administration (TSA) and U.S. Immigration and Border Control at U.S. airports and entry points to make processing security and immigration faster and more secure.
Education: Provide campus safety through controlled access to buildings and dormitories.
Industrial Sites: Ensures only authorized personnel enter hazardous or secure zones.
How Facial Recognition Access Works
What is facial recognition and how does it work? Facial recognition for access control works using the same technology as Apple FaceID and other systems to unlock smartphones using your face. The only difference is that instead of carrying face identification information for just one smartphone user, facial recognition access control includes a database that stores the facial features of multiple users of the same building – sometimes as many as tens of thousands of users.
Behind the scenes, the technology for face recognition access at building doors follows a typical set of steps.
- Face Detection: One or more cameras and visual sensors capture the image or video of a person approaching the access point.
- Feature Extraction: Key facial features (e.g., eyes, nose, and jawline) are analyzed and converted into a mathematical template. Each template has a uniqueness of about one in a million, much like a fingerprint. Even identical twins can’t easily trick some systems.
- Comparison: The captured template is compared against a stored database of enrolled users.
- Verification: If the system finds a match, it sends a signal to unlock the door or open a gate. If not, entry is denied. With many systems, the steps all happen within 2 seconds.
- Continuous Improvement: Many systems use AI to improve recognition accuracy over time, even accounting for changes in appearance.
Benefits of Facial Recognition Access Control
- Touchless Convenience: Enhances hygiene and user convenience with no need for physical keys, cards, or PINs.
- High Security: Difficult to spoof, particularly with advanced 3D recognition systems. Unlike systems with physical keys, your unique face can’t be lost or stolen.
- Speed and Efficiency: Fast identification reduces entry bottlenecks in high-traffic areas.
- Audit Trails: Records access logs for better monitoring and accountability.
- Scalability: Easy integration with existing security systems.
Potential Drawbacks
- Privacy Concerns: Storing and processing biometric data raises data privacy risks, though many systems include a fully encrypted database.
- Accuracy Issues: Poor lighting, facial obstructions (masks, sunglasses), or aging may affect performance on some systems. Systems that use multiple cameras, have depth-perceiving sensors, or include a built-in light can avoid these accuracy issues.
- Cost: Advanced systems can be expensive to implement, but options are available at a wide range of prices.
- Vulnerability to Spoofing: Lower-end single-camera systems may fail to detect photos or deepfakes. Photos can’t fool higher-end systems using multiple cameras and depth perception.
Types of Facial Recognition Access Control Systems
- 2D Facial Recognition: Uses flat images of the face taken by a single camera. This is often found in low-security systems. It is cheap but less secure.
- 3D Facial Recognition: Captures facial contours using infrared sensors or two cameras side-by-side that can perceive depth (like the pair of human eyes). These offer higher accuracy and security.
- AI-Enabled Facial Recognition: Utilizes machine learning algorithms to improve recognition accuracy and adapt to changes in appearance.
- Cloud-Enabled Systems: Store facial data on secure cloud servers, enabling centralized access control management. These systems are great for multi-building campuses so that a central database provides access at multiple doors and entry points.
- On-Premise Systems: Data is stored locally on the intercom device, preferred for environments with stringent privacy concerns.
- Hybrid Systems: Combine multiple recognition technologies for enhanced security and flexibility (e.g., combining facial recognition with PIN or card access).
Facial recognition access control is transforming security management, offering a balance between convenience and high security while requiring careful consideration of privacy and cost implications.
Weather Protection and Anti-Vandalism Durability
Many access control systems are mounted outdoors at the main entrances to buildings. For this reason, the device needs to be rated against a wide range of weather conditions, including humidity/rain and dust, and against physical shocks such as acts of vandalism.
Weatherproofing: For weather, check the hardware’s Ingress Protection (IP) rating. The first digit indicates resistance to dust and the second digit to water. For most weather conditions, look for an IP rating of 65 or higher, which is completely sealed off to dust and which will prevent water entry in any situation except outright flooding that submerges the device. For flood-proof devices, look for IP67 or IP68, though this is only needed for the most extreme conditions.
Anti-vandalism: For protection against physical damage, including vandalism, look for a high Impact/Kinetic (IK) protection rating of at least IK8, though we recommend the highest level, IK10 to protect your investment, especially for high-traffic urban environments.
Ten Top-Tier Makers of Facial Recognition Access Control
As facial recognition technology becomes more widely available, a growing assortment of access control manufacturers are incorporating it into their building intercoms and door control systems. We take a look at ten hardware makers that are well-regarded for their facial recognition enhanced access control systems. We look at the company’s main product with facial recognition and highlight key features.
1. Swiftlane
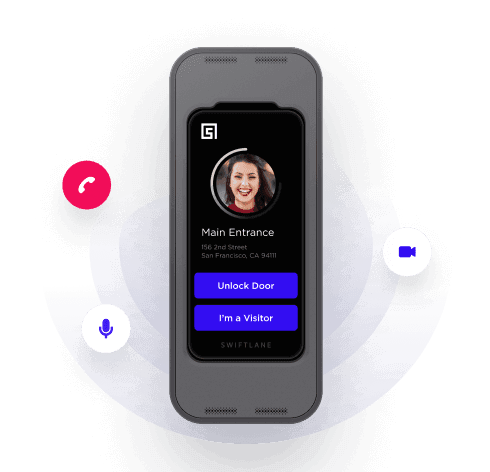
Known For: Swiftlane specializes in touchless access control systems for modern buildings. They integrate AI, facial recognition, and cloud-based management to provide secure, frictionless access solutions. Swiftlane intercoms have a sleek design to enhance the front elevation of any building.
Product: Swiftlane’s Swiftreader X video intercom system incorporates facial recognition, mobile credentials, and PIN-based access, ensuring secure entry with an easy-to-manage cloud platform. It’s widely used in multi-tenant buildings and offices.
- 2D and 3D camera and infrared sensors
- Built-in NFC and BLE mobile access
- Optional RFID key fob, ID badge reader, PIN code access
- IP65 and IK10 ratings (highest anti-vandalism rating)
- Large screen (8”) providing 2-way video
- Compatible with third-party access solutions like Amazon Key for Business
2. ASIS Technologies
Known For: ASIS Technologies specializes in advanced security and access control systems for industrial and commercial environments. They focus on biometric solutions and cutting-edge access control technologies.
Product: The AFR9000 Face Recognition Terminal & Video Intercom Door Station features dual cameras for accurate 3D live facial detection. It offers secure video intercom capabilities and high-speed facial recognition, ideal for environments requiring tight access control.
- Small screen (3.5”)
- Dual camera 3D face detection
- IP67 weatherproof
- Works with RFID card and PIN code technology
- Can handle 10,000 users
3. Akuvox
Known For: Akuvox is a global leader in smart intercom and communication solutions. Their products integrate artificial intelligence, facial recognition, and touchless technology to modernize access control and building communication.
Product: The Akuvox R29C is a touchscreen door intercom equipped with facial recognition, dual cameras, and multiple authentication methods. It ensures secure, touchless access for both residential and commercial applications.
Notable Features:
- Medium-sized touchscreen display (7”)
- Built-in RFID reader for cards or fobs
- IP65 weatherproof rating
- Provide QR codes for temporary access to visitors/guests
- Different built-in modes for single-family homes, multi-dwelling residences, and commercial buildings.
- Can handle thousands of users
4. Abus
Known For: Abus, a German company, is renowned for high-quality security technology, including locks, surveillance systems, and smart building solutions. They emphasize innovation in residential and commercial security.
Product: The Abus FaceXess video door station provides facial recognition technology for seamless keyless entry. It automatically unlocks doors using precise facial scanning, ensuring a convenient and secure access solution.
- IP65 weatherproof rating
- Mid-size (7”) touchscreen
- Access with PIN codes or NFC cards/devices capable
- Limited user capacity: Up to 10 residences
5. Alocity
Known For: Alocity focuses on cloud-based access control and AI-powered security solutions. They deliver intuitive systems for property management, combining facial recognition, video intercoms, and visitor management.
Product: Alocity’s AI1000 video intercom integrates facial recognition with access control, offering real-time management via a cloud dashboard. This enhances security in commercial and residential buildings with touchless access.
Key Features:
- Dual camera 3D face recognition
- Large (8”) touchscreen
- IP65 weatherproofing
- Cloud-based management database
- Integration for PIN code, QR code, RFID fob and mobile app entry
6. Artec ID
Known For: Artec ID specializes in biometric technology, mainly 3D face recognition access control systems. Their solutions are used for secure access to offices, restricted areas, and industrial gateways.
Product: The Artec Intercom 3D leverages 3D facial recognition to provide fast, secure access control. It eliminates unauthorized entry through advanced live face detection, ensuring high-security performance. The system has one of the largest display screens in the industry.
Key Features:
- Large (12”) touchscreen
- Built-in functions for RFID credentials
- Can handle 30 unique users per minute
7. Intelbras
Known For: Intelbras is a Brazilian company known for electronic security, communication, and automation systems. They offer reliable solutions for residential and corporate market.
Product: The XPE 3200 IP Face is an outdoor facial video intercom designed for residential condominiums and commercial use. It features high-speed facial recognition, robust weather resistance, and advanced integration capabilities.
Key Features:
- Dual-camera 3D facial recognition
- Up to 10,000 users
- Built-in RFID credential reader
8. Hikvision
Known For: Hikvision is a global leader in surveillance, security cameras, and smart access control systems. They integrate AI, facial recognition, and cloud technology to provide top-tier security solutions.
Product: The DS-KV9503-WBE1 combines facial recognition, video intercom, and access control in a single device. It is ideal for residential and commercial settings where seamless and secure door access is essential.
Key features:
- Small (4.3”) video screen
- 2-camera system with 3D face modelling
- IP65 and IK08 ratings
- Optional PIN code, ID code, QR code, and Bluetooth entry
9. Indemia
Known For: IDEMIA, formerly known as OT-Morpho, is a French multinational technology company specializing in identity-related security services. The company provides biometric identification products and software, including facial recognition systems, to both private companies and governments. IDEMIA’s solutions are utilized in various sectors, such as security, identity management, criminal justice, border control, banking, telecoms, access control, and public safety.
Product: The VisionPass is IDEMIA’s advanced facial recognition terminal for secure and efficient access control. It offers reliable and accurate identity verification in less than a second, even in challenging conditions. VisionPass is suitable for various applications, including corporate offices, industrial sites, and other high-traffic areas requiring secure access.
- 2D, 3D, and Infrared Cameras
- Mid-size (7”) touchscreen
- Up to 20,000 users
- Mask detection
- IP65 and IK08
- Card reader, PIN code and mobile device compatibility
- Medium (7”) touchscreen
10. Suprema
Known For: Suprema, established in 2000 and headquartered in Seongnam-si, South Korea, is a leading global provider of security and biometrics solutions. The company specializes in access control systems, time and attendance solutions, and biometric technologies, including facial and fingerprint recognition. You can utilize Suprema’s products across various industries, such as construction, healthcare, and data centers, enhancing security and operational efficiency.
Product: The FaceStation 2 is an advanced facial recognition terminal with high-speed matching, accuracy, and security. Powered by Suprema’s latest facial recognition algorithm and a 1.4 GHz quad-core CPU, it provides a matching speed of up to 4,000 matches per second. The device operates effectively in various lighting conditions, ensuring uninterrupted facial recognition in diverse environments.
Key features:
- Infrared and 2D camera
- NFC and BLE mobile access
- Optional fingerprint scanner or RFID card reader
- IP65 weather rating
Frequently Asked Questions
How do access control systems verify identity?
Most access control systems verify identity by issuing each authorized user a credential. Credentials can include a unique PIN code for each user, ID badges, key fobs, or plain-old metal keys. More high security systems can use biometrics, authenticating each user via methods like fingerprint, iris scan, or facial recognition.
Why choose a facial recognition access system over a traditional system?
Other access control credentials like keys, key fobs, ID badges, and even mobile devices can be stolen and used by unauthorized individuals. But it is hard to steal someone’s face! Facial recognition offers one of the most fool-proof methods to ensure the person at the door is who they say they are. It is also a hygienic, hands-free authentication method compared to fingerprint scanning.
Are facial recognition systems reliable?
Facial recognition access control systems that have 3D depth perception are quite reliable. You can’t spoof them by a photograph or screen image of a person’s face, because the system detects that it’s a flat surface. Like fingerprints, our faces have unique features that are unique to us. Even most identical twins have slightly unique facial attributes that facial recognition systems can differentiate.
Can someone try to use a photo of me to gain access to the building?
Most face recognition readers include anti-spoofing technology. For example, with Swiftlane, the SwiftReaders check the 2D and 3D depth data of a face, as well as several other factors. The Swiftlane deep learning algorithms check against this data and prevent people from getting in by holding a photo of a person.
How much does Swiftlane cost?
Unlike most facial recognition access companies in the market that cost upwards of $10,000 per reader, Swiftlane is far more affordable and a Swiftlane system costs the same price as installing a key card-based system. Swiftlane system falls on the lowest end of the price point, starting around $1,300 per door.
More About Swiftlane

Since our founding, Swiftlane��’s access control products have all offered high-quality video intercoms with built-in facial recognition. Facial recognition access control is our specialty. We grew in the market during the early phases of the COVID-19 pandemic when building managers were looking for hygienic and hands-free solutions to provide building access. Now, our products have performed door access over 1 billion times. Find our products in over 1,000 multi-tenant apartment and condo buildings in 45 states, available through over 200 installation partners.
Need More Info?
Still have questions about face recognition access control for your facility? Contact a Swiftlane expert to navigate your options and the best solution.