A good chunk of property upselling depends on its access control system, typically one that offers both high-grade security and convenience. With newer technology vying for attention, you must be selective about the devices you choose for your property. Among a growing range of access control solutions for multifamily security, key fob systems have become a gold standard.
Key fobs help you manage who comes in and out of a building and are an excellent replacement for outdated metal keys. These access control devices are easy to use, have encrypted credentials for trackability, and work on RFID technology.
Today’s key fob systems also integrate with cloud-based platforms, mobile apps, and smart intercoms, letting you control access remotely and ensure only authorized individuals can enter.
Swiftlane has worked with property managers in installing key fob systems as part of their access control infrastructure. We’ve observed how these systems function in the real world. That’s why we’ve curated this guide for property owners, managers, and board members of co-ops, condos, and HOAs who want to modernize their access control systems.
We’ll break down everything you need to know so you can make informed decisions and maximize your property’s NOI with smart building security.
Key Takeaways
- Choose a key fob system for apartments that balances security and convenience for residents and property management staff alike.
- To be flexible, consider a hybrid solution that supports both key fobs and mobile credentials.
- Invest in encrypted key fobs or biometric options if you’re managing a high-security building.
- Streamline your operations by installing a system that integrates with other building technologies, like video intercoms and property management software.
- Work with a trusted provider or installer to ensure a smoother setup and easier long-term maintenance.
Table of Contents
- What Is an Apartment Key Fob System?
- Key Fob Systems vs. Mobile Access for Apartments
- What Are the Different Types of Key Fobs?
- How Do I Know Which Key Fob to Choose?
- Major Manufacturers of Apartment Key Fob Systems
- What Challenges Do Property Managers Face With a Key Fob System for Apartments?
- Installing a Key Fob System for Apartments
- How Much Does a Key Fob System Cost?
- Integration With Modern Building Technology
- Why Choose Swiftlane for Apartment Key Fob Access?
- Frequently Asked Questions
Related Posts
- Key Fob Entry Systems – A Complete Guide
- What Is a Fob System and How to Choose One
- Key Card Entry Systems
What Is an Apartment Key Fob System?
An apartment key fob system is a physical access control system that uses key fobs and an electronic key. The fob serves as a credential that allows authorized persons to access the common areas of an apartment or condominium building.
It can also serve a similar purpose in a gated community or any residential campus. You can find fob use cases at vehicle entryways, pedestrian gates, and shared-use facilities like a clubhouse or pool here.
In residential key fob systems, residents are typically issued quarter-sized key fobs. You can also call these key tags, and they fit on their key ring. You can also use credit card-shaped keys, which are more common in commercial buildings or hotels/motels. Residents “tap” their key tags near a proximity reader built into the wall at various building doors and gates.
Longer-range battery-powered key fobs can also open doors or vehicle gates from a greater distance. Meanwhile, RFID stickers are a kind of fob that can be placed on vehicles to open driveways and parking area gates as the car approaches.
Key fobs are great for residential properties. Residents can use a single fob at multiple entry points, including the main door, a mail room, lounges, and parking areas.
You can also issue key tags to building staff and frequent delivery people. Using these, they can provide maintenance or safely deliver packages indoors without hiring full-time door or gate staff.
How Do Key Fobs Work for Apartments?
A proximity reader installed at building entryways sends a radio wave on common frequencies. You may have heard of these as radio frequency identification (RFID), near-field communications (NFC), and Bluetooth Low Energy (BLE).
The credential sends a signal back to the reader, which the reader cross-references with a system database. If the credential has been authorized to open that particular door or gate, it opens using a magnetic or electronic door lock mechanism.
Are Key Fobs Safe for Apartments?
Key fobs for apartments have many security benefits but also a few notable shortcomings. Overall, they are a safe choice for access control that can enhance residential building security. Like other lock mechanisms, they are not fool-proof.

Safety benefits include:
- Security records: Each resident is allocated a unique key fob, and their times of entry can be recorded in a database. Building management can use credentials linked to the user database to track who is coming in and out, the time of entries, and get overall data about building traffic.
- Intercom integration: Key fob systems can be part of a telephone call box or, better yet, a video intercom. This gives residents a way to screen visitors and keep the building safe.
- Remote deactivation: You can deactivate key fobs remotely when someone moves out or when a key fob is reported lost or stolen. This means you can keep the building secure without changing the locks.
- Touchless entry format: Post-COVID, it has become natural for people to avoid common surfaces. Key fobs work over radio waves and provide a contactless way to get into a building (unlike devices that require you to push a button).
- Granting limited access: Not everyone requires access to all common spaces. With key fobs, you can restrict tenants’ access to certain areas (poolside, gym) and enable time-specific access.
Safety disadvantages are:
- Many can be copied: You can copy most key fobs using equipment available on the Internet, which basically exposes your property to anyone who has the know-how. Fobs aren’t a foolproof security method if you have high-security needs. Facial recognition prevents this problem to a large extent by relying on unique biometric traits.
- Most work in short ranges: It isn’t really a benefit if you still have to fish for a key fob within your bag like you do with a physical key. With most fobs, you need to tap the device on the reader to gain entry, although you can get a long-range key fob at a higher price.
- Higher cost: You need a unique key fob for each tenant to access the building independently. If your building has multiple units, key fobs build up a significant cost for management.
Key Fob Systems vs. Mobile Access for Apartments
While key fob systems remain common, many are now evaluating mobile credentials as part of a broader access control strategy. Instead of choosing between these two options, why not just implement a hybrid system that can support both?
Through NFC or Bluetooth technology, mobile access systems allow residents to unlock doors using their own smartphones. They won’t need to carry a separate device, you won’t need to issue a physical credential.
Here’s a side-by-side comparison between key fobs and mobile access:
| Feature | Key Fob System | Mobile Access System |
| Credential Format | Physical fob, card, or tag | Smartphone (NFC or Bluetooth) |
| Upfront Credential Cost | $5 to $50 per fob depending on encryption | No physical credential cost |
| Replacement Cost | Moderate to high (lost or unreturned fobs) | Zero (residents rarely lose smartphones permanently) |
| Remote Provisioning | Varies by system; may require on-site programming | Instant and remote |
| Guest Access | Requires issuing physical credential | Temporary digital passes can be issued remotely |
| Audit Trail Visibility | Standard entry logs | Real-time cloud-based logging |
| Connectivity Requirements | Works without cellular service | May require internet or Bluetooth connectivity |
| Resident Adoption | Familiar and widely accepted | Highly preferred by younger residents and becoming an expected credential format in most modern properties |
| Long-Term Scalability | May require hardware expansion | Easier to scale across portfolios |
Bottom line: Key fobs remain reliable and familiar. They work well in garages and for residents who prefer physical credentials.
On the other hand, mobile access eliminates credential replacements and allows for faster onboarding (users can just download the app to their smartphones). To learn more, download our guide for a deep dive into the benefits of mobile access.
A more practical approach might be a hybrid system that lets residents choose their preferred credential. At the same time, this gives you flexibility in catering to tenants’ needs.
What Are the Different Types of Key Fobs?
Passive vs. Active Key Fobs
- Passive key fobs grant access without pressing any buttons. They work only when they’re close to the access point, such as by “tapping” it at the proximity reader.
- Active key fobs are battery-powered and send signals over longer distances (up to 100 feet) using the same technology as a remote car key with lock/unlock buttons. They necessitate user intervention by physically pressing a button on the fob to unlock the access point.
Unencrypted vs. Encrypted Key Fobs
Not all key fobs offer the same level of security.
- Unencrypted key fobs store their access credentials in plain text, making them vulnerable to duplication. Anyone with access to a cloning device (which can easily be bought online) can copy an unencrypted fob in seconds, creating a major security risk.
- Encrypted key fobs use advanced communication protocols to send secure, scrambled data between the fob and the reader. This encryption makes it nearly impossible to duplicate a fob without authorization, significantly reducing the risk of unauthorized access.
Car RFID Tags
A comprehensive residential key fob system can include RFID tags for cars, which trigger gates to open at driveways, neighborhood entry points, or parking garages without the driver having to lean out the window to use their key tag.
These small stickers or tags, typically placed on a car’s windshield or near the license plate, automatically trigger a proximity-based RFID reader to open the gate as the vehicle approaches.
This hands-free solution is especially useful in high-traffic areas where manual key fobs may slow your entry. Plus, because each tag is uniquely assigned to a vehicle, property managers can track who comes and goes and easily deactivate lost or stolen tags for enhanced security.
Mobile Phones
Using mobile phones as fobs is the future of access control. Using the same “tap to pay” technology built into today’s smartphones, you can use your phone to grant you entry, saving you the trouble of carrying a separate fob. Mobile phones are also encrypted, making it extremely hard to make an illegal copy of your phone as a key tag.
How Do I Know Which Key Fob to Choose?
If you are investigating apartment key fob systems, you’ll want to keep in mind the following features and characteristics:
Key Fob Security Level
Standard 125 Khz key fob systems are the cheapest because they use standard generic unencrypted key fobs. However, they are easy to copy and don’t provide the highest level of security. Buildings with high-profile residents may want to invest the extra money in key fob systems that use encrypted technologies like MIFARE DESFire or 13.56 Mhz.
Key Fob Type
Many apartment key fob systems can work with multiple types of credentials so that you can choose the best credential type for your residents. They include key tags, key cards, or, these days, using a mobile phone as the credential. With many systems, you can also issue stickers, which can function as vehicle tags.

System Integration and Features
When evaluating a key fob system, look beyond the fobs and consider how the system fits into your building’s overall access control setup.
Some office properties already have infrastructure in place, such as electronic door strikes, intercoms, call boxes, or security cameras.
In those cases, confirm that the key fob system can integrate with the equipment already installed so you don’t have to replace hardware that’s still working.
If you’re upgrading from traditional locks or an older access control system, it may make more sense to deploy a modern access control platform that already supports key fobs along with other entry methods.
Look for systems that offer features like PIN keypad entry, video intercoms for visitor access, and remote management software. These tools make it easier to manage multiple entry points across the building, including lobbies, parking areas, shared amenities, and restricted spaces.
Cost
The cost of a basic key fob system depends on the hardware required at each door.
For a simple single-door setup, hardware may include:
- RFID reader: $150 to $300
- Door controller or access panel: $150 to $400
- Key fobs or credentials: $5 to $20 per fob
Once these components are combined, a basic entry point can cost a few hundred dollars before installation.
More integrated systems cost more depending on the hardware involved. For example, systems that combine video intercoms, key fob readers, and remote management software typically range from $1,500 to $5,000 per entry point, depending on features and installation complexity.
Installation costs are separate. Some key fob systems require additional hardware on-site to run the software and system database, while others operate in the cloud, usually for a monthly subscription fee.
Capacity
Check whether your potential key fob system can scale to the number of potential users in your building. As your properties expand manifold, scalability is an important consideration to keep in mind while purchasing an access control system.
Key Fob Software and Programming
If you are looking for a new installation of a key fob system, we suggest you look for systems with cloud-based remote management software to program the system.

Older apartment key fob systems required a computer installed at each building, often with clunky software to manage the database of key fobs. Someone would have to physically go to this computer and add or remove each user as people moved in or out or if a fob became lost or stolen.
Many key fob system providers today offer a cloud-based management platform that building managers can log into from any computer. This saves building managers significant time and labor from programming key fob systems at each entry point, especially if they manage multiple buildings. System providers typically charge a monthly subscription fee to use these platforms, which you can easily recoup in reduced operating costs.
Major Manufacturers of Apartment Key Fob Systems
We provide a sample of major manufacturers specializing in apartment key fob systems. However, there are dozens of potential manufacturers beyond this list of some of the biggest names.
Swiftlane
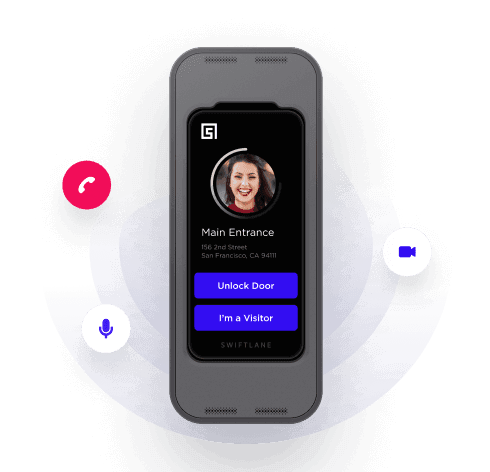
Swiftlane provides modern access control solutions for apartments and mixed-use properties. Its platform supports key fob systems, as well as mobile credentials and facial recognition access. With its video intercom panels and centralized management tools, it can offer multiple secure entry options while allowing you tight control over apartment access.
Aiphone
Aiphone is a global manufacturer of intercom and access control solutions used in multifamily properties. They offer video intercom platforms for apartments that support key fob credentials. Their systems can combine door stations, video comms, and centralized management tools.
HID Global (part of ASSA ABLOY)
HID Global provides RFID credentials used in many key fob systems for apartments. Known for its smart cards, encrypted fobs, and mobile access solutions, HID supplies credential technology, including encrypted key fobs that integrate with various access control platforms. Their products can be used in multifamily properties, with options that range from basic 125 kHz fobs to high-security encrypted credentials.
DoorKing
DoorKing focuses on telephone call box entry systems for large apartment complexes. Known for their durability and ability to withstand harsh weather, DoorKing offers three models that include key fob access, although these systems don’t have video capabilities.
What Challenges Do Property Managers Face With a Key Fob System for Apartments?
Move-In and Move-Out Turnover
Each new resident requires credential issuance, and each departing resident requires deactivation. In high-turnover buildings, this can become a daily administrative task.
Lost or Unreturned Fobs
Residents occasionally lose key fobs or move out without returning them. Yes, replacing a single fob isn’t expensive. But the costs and administrative work can add up over time.
Property managers also need to ensure lost credentials are quickly deactivated to prevent unauthorized access to the building.
Amenity Access Management
Pools, gyms, coworking spaces, and package rooms may require restricted or time-based access. Managing these permissions manually can be complex when you don’t have a centralized access control system.
Staff and vendor credential control
Limited access is best for maintenance staff, cleaners, and contractors. If they’re not properly configured, credentials may remain active longer than you originally planned.
Multi-Property Oversight
When you’re managing multiple properties, it may be costly and time-consuming to conduct on-site programming for older, legacy systems.
The challenges listed above highlight the importance of choosing a centralized access control platform that simplifies credential management and allows remote administration.
Installing a Key Fob System for Apartments
Many companies manufacture key fob system hardware and components like electronic door strikes, call boxes, and intercoms.
However, the actual installation is often handled by third-party companies, known as “system integrators,” located across the country. Installing these systems is typically not a DIY project unless your residential property has an in-house staff skilled in electrical engineering and security system setup.
Most access control systems require wiring to connect them to the building’s power supply and the door release mechanism. Systems that use cloud-based databases may also need an internet connection.
Most hardware manufacturers can recommend experienced installation companies familiar with their products in your area.
How Much Does a Key Fob System Cost?

A single-entry key fob setup usually costs a few hundred dollars before installation. You’re looking at $150 to $300 for the reader, $150 to $400 for the door controller, and $5 to $20 per fob.
If you want video intercoms, cloud management, or multi-door setups, expect $1,500 to $5,000 per entry point. Installation is extra, and cloud-based platforms may add a small monthly fee. But they make managing multiple doors or buildings much easier.
Professional installation fees vary based on location and complexity, such as whether you need one or multiple entry points. Your system integrator or hardware provider can provide a detailed quote. If you want a starting point for pricing, consider getting a quote from Swiftlane.
Integration With Modern Building Technology
More and more apartments nowadays operate as integrated ecosystems instead of being standalone systems.
When evaluating a key fob system for apartments, consider how it integrates with:
- Video intercom systems
- Elevator access control
- License plate recognition systems
- Security cameras
- Package room access control
- Property management software
There are many ways integrated systems can streamline your operations:
- If you link access credentials to property management software, you can simplify onboarding for new residents.
- You can integrate elevator control to restrict floor access to authorized residents only.
- Connecting security cams to entry logs can aid in incident investigations.
Choosing a system that supports integration can reduce future upgrade costs and make property management more efficient.
Pro tip: The National Multifamily Housing Council makes it clear: properties shouldn’t lock themselves into one credential type. A modern key fob system for apartments should also support mobile access and integrate easily with other building systems, so you’re not stuck replacing everything in a few years.
Why Choose Swiftlane for Apartment Key Fob Access?

- Our key fobs are part of a video intercom system that allows residents to screen visitors and remotely unlock the doors from anywhere using their smartphones.
- Residents can gain access to doors using facial recognition (optional), meaning they don’t have to fish out their key fob most of the time.
- Use your smartphone as the key fob with no additional equipment.
- Building management can use our cloud-based management platform to control the system, add and remove users, and change resident permissions remotely.
Get a quote from us and learn more.
Frequently Asked Questions
Can I program an apartment key fob myself?
Building managers/owners CAN typically program an apartment key themselves, once the system is installed. Your installer will give you the necessary hardware and software so that you can manage the system and add or remove users and give out new key fobs to residents as needed.
If you are a building resident, you typically CAN’T program a key fob by yourself since you need access to the management software.
Can you copy a key fob?
Copying a key fob, also known as “cloning,” is not as easy or straightforward as copying metal keys at any local hardware store. It requires specialized RFID reader equipment that most people or stores don’t carry but that you can easily purchase online.
What signal do apartment key fobs use?
Key fobs use various types of radio waves to communicate between the proximity reader and the credential. Radio standards used include RFID, NFC, Bluetooth LE, and the older Wiegand protocol. These all use safe frequencies that have been in use for decades and have not been demonstrated to pose any health risks.
What do I do if I lose my key fob?
If you are a building resident who has lost your key fob, contact your building owner or manager. They have access to the key fob system’s backend and can create a new key fob credential.
Can I be tracked from my key fob?
Generally, no. Your apartment key fob can’t be used to track you. Key fobs don’t have GPS or integration with WiFi or cellular networks, so they can’t be used to follow someone from place to place once they leave your residence.